Using Out of Office / automaticRepliesSetting with the Microsoft Graph with Service Principal Authentication
Out of Office (or automaticRepliesSetting) can be used for a vast number of different applications. For example in this Teams In/Out board
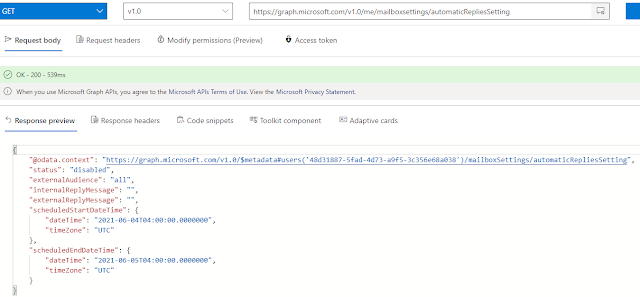
With the Microsoft Graph API there are two ways that can be used to get the automaticRepliesSetting either via the Mailbox setting Endpoint eg
https://docs.microsoft.com/en-us/graph/api/resources/automaticrepliessetting?view=graph-rest-1.0
eg
What is better ? for getting the OOF settings on a large number of users getmailtips because you can request up to 100 users in one request while if your batching Mailboxsetting you can only have a max of 20 user in a single batch.
Permission and Authentication
One consideration for the Mailboxsettings endpoint is there is no ability to use Delegate permissions to access the Mailbox settings of a user other then that of the credentials (unlike EWS where you could use delegation). So for most use cases (eg daemon apps or other automation back-ends) you will need to use Service Principal authentication and Application permissions. This can open up some security concerns if the application in question is only required to work on a subset of Mailbox make sure that you employ scoping
So to use this function you first need to acquire the local certificate which could be either stored in the Local Certificates Store or in a PFX file with a password. eg
Using Service Principal Authentication in Power Shell
I don't yet have a sample for doing this in my Graph 101 series but its actually less complicated then doing an authentication code type auth because all your code needs to do is create a JWT token from a locally stored SSL certificate (and sign it). Here is some sample code for doing this
So to use this function you first need to acquire the local certificate which could be either stored in the Local Certificates Store or in a PFX file with a password. eg
$certificate = Get-ChildItem -Path Cert:LocalMachine\MY\FCE7328421DDDB4CC8EA59C51B6F156765272CFA
or from a PFX file
$certificate = Get-PfxCertificate -FilePath C:\temp\certo.pfx
Once you have the certificate you can then request the token like
Get-AccessTokenForGraphFromCertificate -Certificate $Certificate -ClientId e6fd6f09-9c63-4b30-877a-3520ee1e1e9a -TenantDomain domain.com
Samples for Getting the AutoReplySettings using Service Principal Authentication
For this post I've put together a sample of Getting the AutoReply Setting for One user and batch of users via the Mailbox Setting Endpoint using certificate Authentication. And also a sample or using MailTips to do the same.
The script for this is available on Github here https://github.com/gscales/Powershell-Scripts/blob/master/Graph101/AutoReplySettings.ps1